- What Are the Windows End-of-Life Business Risks?
- Can Windows End-of-Life Put You Out of Compliance?
- Does Delaying Windows Upgrades Increase IT Costs?
- Will Older Windows Versions Cause Compatibility Issues?
- How Does Windows EOL Impact Business Productivity?
Learn how to protect your business before it’s too late!
Understanding Windows End-of-Life Business Risks
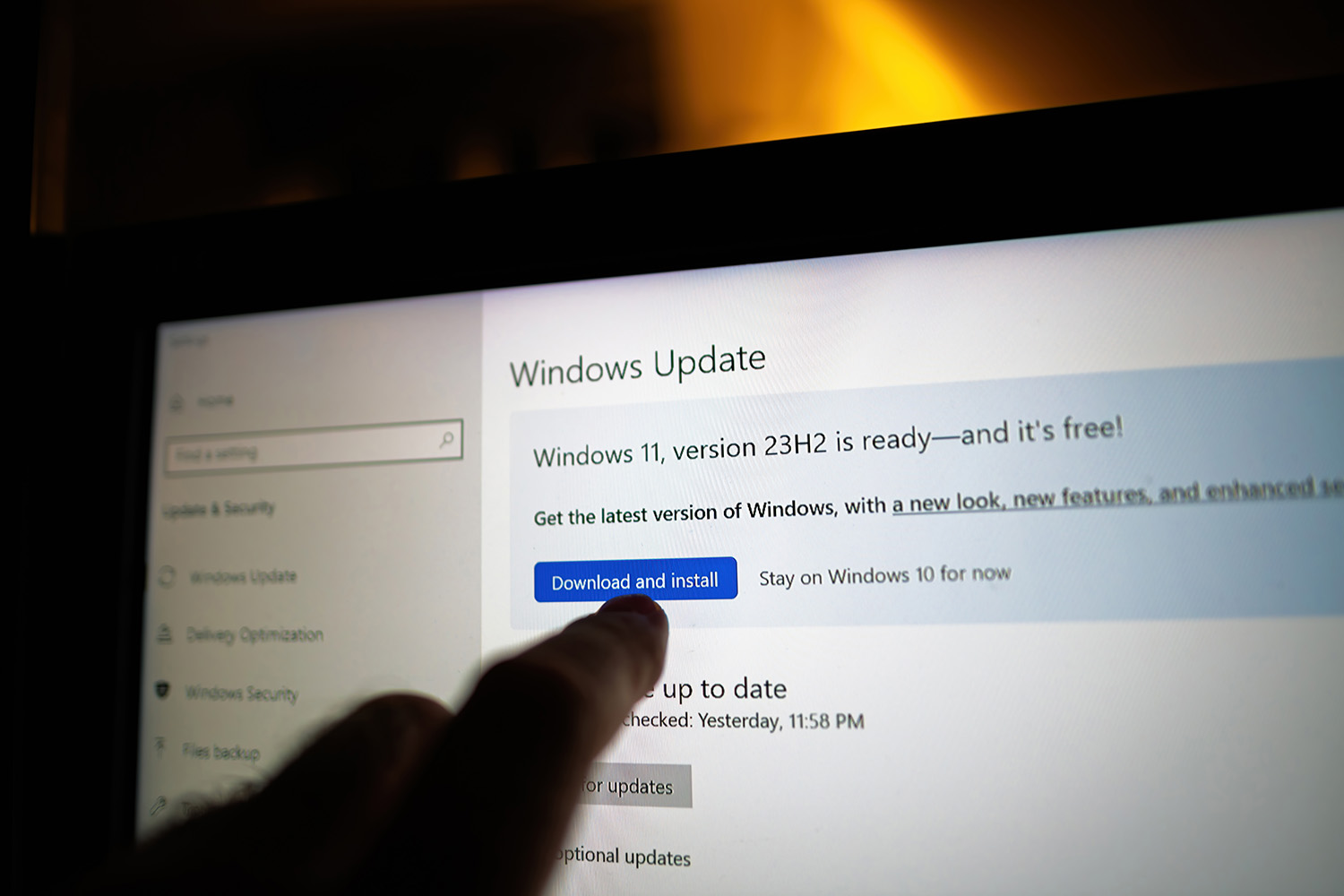
Is your business still using an older version of Windows? This might be working out reasonably well for you, but have you ever thought about what might happen when Microsoft stops supporting it? For businesses in Willow Grove, PA, this isn’t just an IT issue; it’s a big business risk that could surprise your bottom line.
When a version of Windows reaches its end-of-life (EOL), Microsoft stops issuing security updates, technical support, and bug fixes for it. This is the setup for a perfect storm of vulnerabilities that cybercriminals are waiting to exploit.
The Harsh Consequences of Ignoring Windows End-of-Life
What happens if you delay your Windows upgrade? Here’s what you could be facing:
- Security Vulnerabilities: The end of regular security patches makes your systems prime targets for malware, ransomware, and data breaches. In Willow Grove, we’ve seen businesses hit by attacks that are aimed specifically at outdated systems, and the result is significant downtime and data loss.
- Compliance Violations: Many regulatory frameworks (HIPAA, PCI DSS, GDPR) require businesses to maintain updated operating systems. Failing to comply can result in hefty fines and reputational damage.
- Compatibility Issues: In many cases, newer software applications and hardware don’t work well with outdated Windows versions, which means you could find yourself unable to adopt innovative tools that could give you a competitive edge.
- Rising Support Costs: Maintaining outdated systems requires specialized knowledge and customized solutions, and you will likely have to pay elevated IT costs as a result.
- Decreased Productivity: Older systems run slower, crash more often, and lack many of the modern features your competitors might be using to enhance efficiency.
Essential Steps to Address Windows End-of-Life Business Risks
Don’t make the mistake of waiting until it’s too late. Here’s how to prepare for your Windows upgrade:
- Conduct a system inventory: Identify all of the devices that are running soon-to-expire Windows versions.
- Assess application compatibility: Determine which of your business applications will work with newer versions of Windows.
- Develop a migration timeline: Create a realistic schedule that will minimize disruptions to your operations.
- Budget appropriately: Don’t just factor in software costs; be sure to include potential hardware upgrades and implementation services as well.
- Train your team: Make sure your employees are prepared for the transition to maximize productivity.
For businesses in Willow Grove, addressing Windows End-of-Life business risks is essential for business continuity, security, and staying competitive.
Are you wondering how to start planning your Windows upgrade? Do you need help understanding what this transition means specifically for your business?
Our team of IT professionals specializes in helping Willow Grove businesses address these technology transitions while maximizing security and minimizing disruptions.
Take the First Step Today
If mitigating these Windows End-of-Life business risks is a priority, this is exactly what our MSP specializes in. Does it make sense to carve out 15 minutes to discuss your next step?
Download our complimentary Windows Upgrade Readiness Guide to understand what your team should prepare for, including best practices and answers to frequently asked questions.
Don’t let Windows End-of-Life business risks pose a threat to your operations. Contact us today to schedule your personalized upgrade assessment.